Passwords: Your Business’s Weakest Link? How to Bulletproof Your Company in 2025

Traditional passwords no longer protect your business. Discover why they are vulnerable and what expert strategies and tools (password managers, MFA, YubiKey) you must implement to bulletproof your systems in 2025.
How Do Websites Use My Data? (Best Practices for Data Sharing)
Websites collect and share user data in ways many people don’t realize—from tracking clicks to sharing info with advertisers. In this post, we explain how data is gathered, why privacy matters, and what you and website owners can do to protect it.
Ultimate Guide to Safe Cloud Storage
Cloud storage makes life easier, but it also brings security risks. In this post, you’ll learn how to choose a secure provider, apply strong protection measures, and stay ahead of threats—so your data stays safe, no matter where you access it from.
Complete Guide to Strong Passwords and Authentication
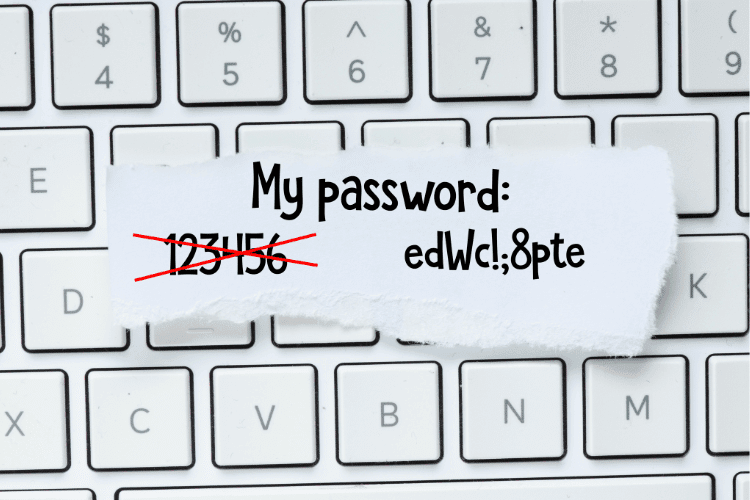
Weak passwords and outdated login methods are no match for modern cyber threats. In this guide, we break down how to build stronger passwords, use multi-factor authentication, and adopt safer habits to keep your accounts secure in a rapidly evolving digital world.
New Gmail Threats Targeting Users in 2025 (and How to Stay Safe)

As AI-powered cyberattacks grow more advanced in 2025, Gmail users face new and sophisticated threats—from deepfake scams to AI-generated phishing and zero-day exploits. This post breaks down the evolving risks and offers clear steps to keep your Gmail account secure.
What is Password Spraying?

Password spraying is a stealthy cyberattack that targets multiple accounts using weak, commonly used passwords—bypassing traditional lockout protections. In this post, we explore how it works, how it differs from other attacks, and what steps you can take to detect and prevent it.
7 Unexpected Ways Hackers Can Access Your Accounts

Hackers aren’t just using weak passwords or phishing emails anymore—they’re getting creative. From SIM swapping to AI-powered phishing, this post reveals 7 surprising ways your accounts could be compromised—and what you can do to stay safe.
Can My Data Be Removed from the Dark Web?

The dark web poses a serious threat to your personal data. Once information is exposed, removing it is nearly impossible. This article explains why—and shows you how to protect your identity and strengthen your digital security.
Where Do Deleted Files Really Go? Understanding File Recovery and Secure Deletion

Think deleting a file means it’s gone forever? Not quite. Learn what really happens when you delete files, how they can be recovered, and why secure deletion is key to protecting your sensitive data.
10 Creative Ways to Personalize Your Desktop and Boost Productivity

Customize your desktop like a pro with these 10 easy tips for Windows, macOS, and Linux. From backgrounds and themes to widgets and automation, discover how to make your workspace more productive and uniquely yours.
